What Is an ATM Jackpotting Attack and How Does It Work?
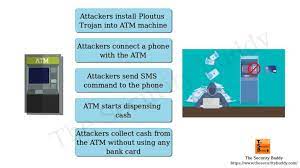
ATM jackpotting attacks are a new type of cybercrime that target automated teller machines (ATMs). In these types of attacks, hackers use a combination of software and hardware to steal cash directly from the machine, often in large amounts.
At the core of an ATM jackpotting attack is malware that is injected into the machine’s operating system. This malware allows the hacker to take over control of the ATM, giving them full access to the cash inside. They can then use a physical device, such as a laptop or mobile phone, to activate the malware and trigger the cash withdrawal process.
Typically, this type of attack requires the hacker to have physical access to the ATM. They may gain access by using a crowbar or other tool to pry open the machine’s casing, or they may simply install the malware via a USB port or network connection. Once the malware is installed, the ATM is essentially a “bot” that can be controlled remotely by the hacker.
To maximize their profit, hackers often target ATMs that are located in high-traffic areas, such as shopping centers or airports. They may also target machines that are located in isolated or poorly-lit areas, where they can carry out their attack without being detected.
One of the key factors behind ATM jackpotting attacks is the relatively low security of many ATM machines. Many older machines are not equipped with the kind of security measures that are necessary to prevent modern hacking techniques. For example, many machines do not encrypt data or use strong passwords, leaving them vulnerable to attack.
Some newer machines have been designed with more advanced security features, such as biometric authentication and tamper-resistant casings. However, even these machines can be vulnerable to attack if the hacker is skilled enough.
As ATM jackpotting attacks become more common, banks and ATM manufacturers are taking steps to improve the security of their machines. This includes deploying software updates and patches that are designed to prevent malware attacks, as well as improving physical security measures such as cameras and alarms.
Overall, ATM jackpotting attacks are a serious threat to the security of ATM machines and the people who use them. By understanding how these attacks work, individuals and organizations can take steps to protect themselves and minimize the risk of falling victim to this type of cybercrime.