What Is a DMZ and How Do You Configure One on Your Network?
As the world becomes more connected and the internet becomes an essential part of our daily lives, data security is becoming increasingly important. One way organizations can protect themselves against cyber threats is by implementing a DMZ (Demilitarized Zone) on their network.
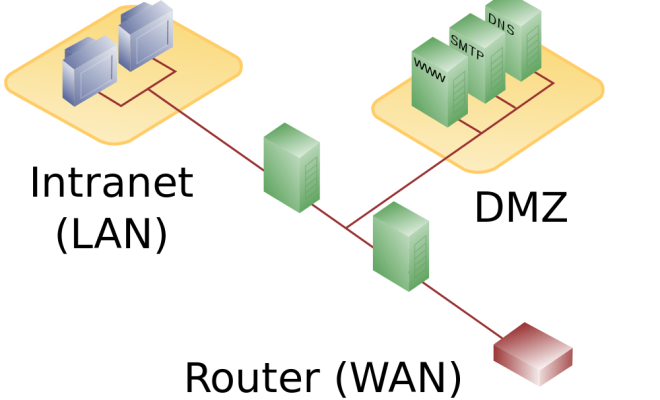
A DMZ is a network segment that separates an organization’s internal network from the internet. It is an area where servers and services that need to be accessed by the public are located, such as web servers, email servers, and FTP servers. By isolating these services in a DMZ, if an attacker were to gain access to the DMZ, they would not automatically have access to the organization’s internal network.
To configure a DMZ, several steps need to be taken. The first step is to decide what services will be located in the DMZ. It is essential to limit the number of services to only those necessary to minimize the number of possible attack vectors.
Once the services are identified, the next step is to create a separate subnet for the DMZ. The DMZ should have its IP address range, which is different from the internal network. Additionally, a firewall should be installed between the DMZ and the internet to control access between the two.
Another important step is configuring access controls for the DMZ. Access should be restricted only to the necessary ports and protocols required for the services in the DMZ to function properly. All other ports should be blocked to prevent unauthorized access.
Finally, all systems on the DMZ should be regularly maintained and updated to ensure they are running the latest software and security patches. This includes operating systems, web server software, email server software, and any other software installed on the servers.
In conclusion, a DMZ is an essential component of a network security strategy. It provides an additional layer of defense against cyber threats and helps organizations protect their internal network from external attacks. By carefully configuring a DMZ and implementing proper access controls, organizations can significantly reduce their risk of a data breach.