What Are WEP and WPA? Which Is Best?
Wireless encryption protocols, such as WEP (Wired Equivalent Privacy) and WPA (Wi-Fi Protected Access), are used to secure wireless networks from unauthorized access. Understanding the differences between WEP and WPA is crucial for selecting the right security protocol for your Wi-Fi network.
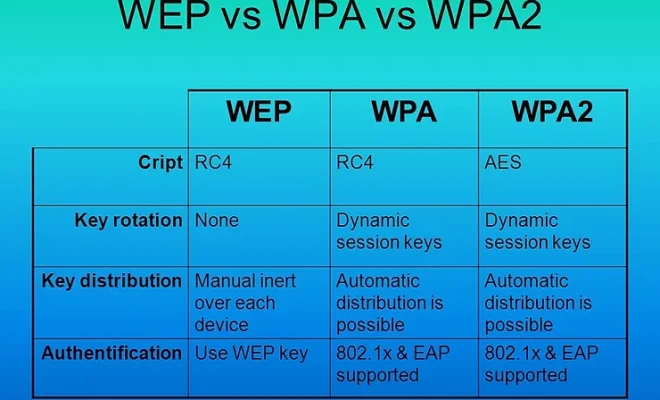
WEP was the first wireless security protocol introduced in 1999, which aimed to provide a level of encryption equivalent to wired networks’ security. WEP encrypts data between devices using a key, but it is considered insecure because it uses a static key, which can be easily hacked. Since WEP’s encryption algorithm is weak, hackers can quickly obtain the keys using a software tool or exploit WEP’s vulnerabilities.
In contrast, WPA was introduced in 2003 to provide a higher level of security than WEP. WPA improves upon WEP by using dynamic keys, ensuring that transmitted data is encrypted using a new encryption key every time a device connects to a network. Additionally, WPA enables mutual authentication, which means that both the network and the device are authenticated before allowing an access connection.
WPA was later upgraded to WPA2, which is currently considered the most secure wireless security protocol. WPA2 further strengthens the encryption algorithm, making it more challenging for hackers to decrypt network traffic. WPA2 uses a robust encryption algorithm called the Advanced Encryption Standard (AES), which makes it an excellent choice for both personal and enterprise use.
So, which is the best protocol to use, WEP or WPA? Without a doubt, WPA and its successor WPA2 are much more secure than WEP. In fact, WEP is no longer recommended due to its many security vulnerabilities, and its use is now prohibited by security standards. If you use WEP, you can be sure that your network is insecure, and it is vulnerable to hacking.
In conclusion, when it comes to wireless security, WPA2 is the best choice. It is the most secure wireless encryption protocol, and it is recommended for all Wi-Fi networks. Choose WPA2 over its predecessors, and always use complex passwords and avoid sharing them with others for maximum security.





