What is vulnerability (information technology)?
The concept of “vulnerability” in information technology refers to a weakness or flaw in a system’s security measures that can be exploited by unauthorized individuals. Vulnerabilities can exist in hardware, software, or network components, and can be caused by design flaws, coding errors, or inadequate security practices.
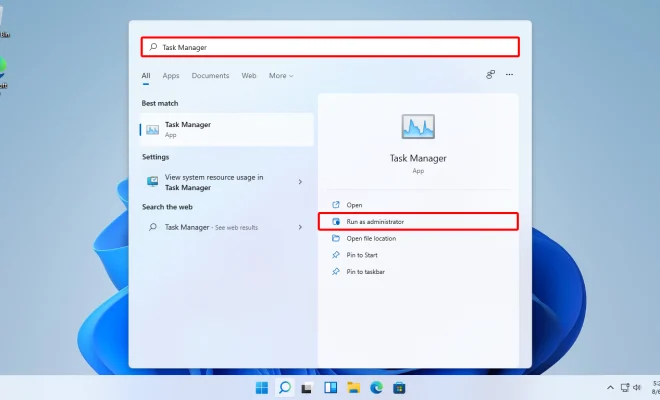
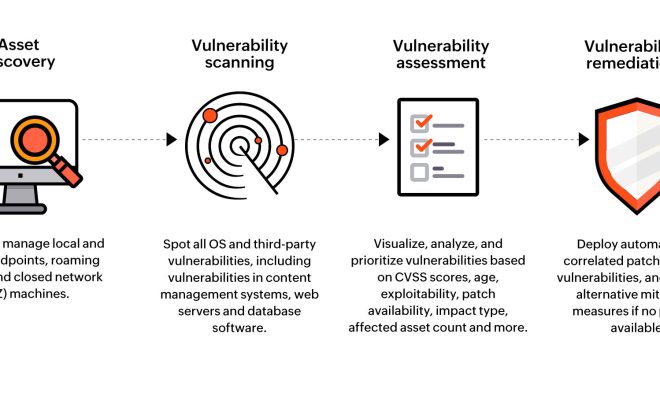
In order to maintain the security of their systems, IT professionals must identify vulnerabilities within their infrastructure and apply patches or updates to mitigate potential risk. Vulnerability assessments and penetration testing are common methods used to identify and exploit weaknesses in an organization’s security posture.
Examples of vulnerabilities include unpatched software, weak passwords, misconfigured firewalls, and social engineering attacks. As technology continues to evolve, so too do the methods and techniques used by attackers to exploit vulnerabilities. Cybercriminals are constantly seeking new ways to infiltrate systems and steal sensitive information, making it critical for organizations to stay vigilant and proactive in identifying and addressing vulnerabilities.
In addition to proactive measures, organizations must also have a robust incident response plan in place to quickly detect and respond to security incidents. This includes measures like monitoring system logs, implementing intrusion detection systems, and regularly reviewing and updating security policies and procedures.