How to choose the best cloud security posture management tools

Choosing the right cloud security posture management (CSPM) tools is critical for maintaining your organization’s cloud infrastructure. As the reliance on cloud environments grows, so does the complexity of managing and securing these platforms. Here are some key points to consider when selecting CSPM tools for your business:
1. Visibility: A robust CSPM tool should offer comprehensive visibility into your entire cloud environment. Look for a solution that provides a unified view of assets across multiple cloud services.
2. Compliance Monitoring: Ensure that the tool can continuously monitor compliance with industry standards and regulations applicable to your organization, such as GDPR, HIPAA, PCI DSS, and others.
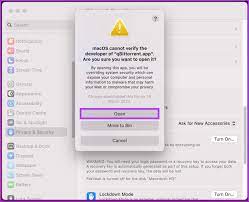
3. Automated Remediation: The ideal CSPM should be able to automatically identify risks and swiftly rectify them without human intervention, thereby reducing the window of exposure.
4. Integration Capabilities: Check if the tool can seamlessly integrate with your existing security infrastructure and workflows, including SIEM systems, incident response platforms, and other IT management tools.
5. Threat Detection: Choose a CSPM solution that leverages advanced analytics to detect threats in real-time by understanding normal behavior patterns and identifying anomalies.
6. Customization and Policy Management: The tool should allow you to define custom policies tailored to the specific needs of your organization and enforce those policies consistently across your cloud environment.
7. User-Friendly Interface: Select a CSPM with an intuitive dashboard that makes it easy for users to understand security postures, view alerts, and access reports without special training.
8. Scalability: As your cloud footprint grows, your CSPM solution must be able to scale accordingly without losing performance or increasing complexity.
9. Support and Training: Top-notch customer support is non-negotiable; also inquire about training resources to ensure that your team can utilize the tool’s full capabilities efficiently.
10. Vendor Reputation and Reliability: Research the vendor’s track record for reliability and customer satisfaction, including case studies or testimonials from clients in similar industries.
11. Cost Considerations: Finally, weigh the total cost of ownership against your budget constraints and expected return on investment (ROI). Be sure to factor in not just licensing fees but also costs associated with deployment, maintenance, and potential scalability options.
By considering these criteria when choosing a CSPM tool, you can better safeguard your cloud environments against vulnerabilities while achieving compliance requirements efficiently.