What is Database Activity Monitoring (DAM)?

Database Activity Monitoring (DAM) is a cybersecurity technology that monitors and audits database activities across different database management systems (DBMS). DAM systems monitor and analyze database activities to detect potential security threats and prevent unauthorized access, data leakage, and data breaches. DAM solutions provide real-time monitoring and alerting of suspicious activities, compliance reporting, and forensic analysis to investigate possible security breaches.
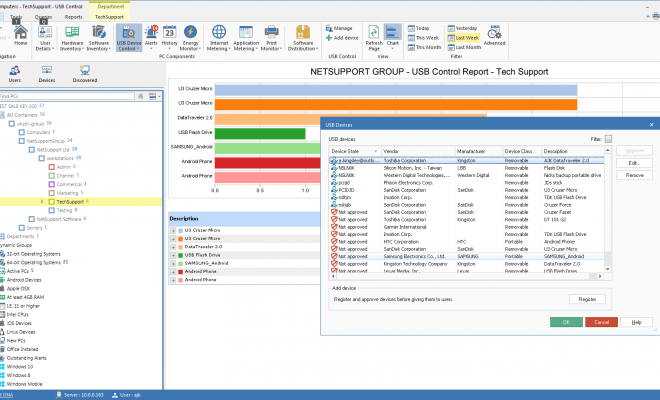
In simple terms, DAM is a security system that monitors all the activities happening in databases, such as creating, reading, updating, and deleting data. It also monitors and audits user activity such as logins, access, and changes to database schema or configuration files. DAM solutions use various techniques such as network traffic analysis, log analysis, behavioral analysis, and policy-based monitoring to detect and prevent security threats.
Typically, database activity monitoring involves the following steps:
1. Collecting and analyzing database events: DAM systems monitor, record, and analyze all events and transactions happening in the database including SQL queries, stored procedures, and data modifications.
2. Correlating events: DAM systems correlate database events with alerts from other security technologies such as intrusion detection systems (IDS) and security information and event management (SIEM) systems to provide a more comprehensive view of security threats.
3. Alerting and reporting: DAM solutions generate alerts in real-time when suspicious activities are detected. DAM also generates compliance reports for regulatory compliance such as HIPAA, PCI-DSS, and GDPR.
4. Investigating security incidents: DAM systems also provide forensic analysis to investigate security incidents and breaches. They offer capabilities to search, correlate, and aggregate events across different DBMS for threat hunting and incident response.
DAM is crucial to securing database infrastructure as SQL injection, privilege escalation, and unauthorized access attempts are common attack vectors used by cybercriminals to gain access and exfiltrate data. DAM solutions can help organizations achieve compliance with various regulatory requirements and standards by providing audit trails, data protection measures, and access controls.
DAM solutions are widely used by organizations of all sizes, especially those in regulated industries such as healthcare, finance, and government. DAM providers offer both cloud-based and on-premises solutions to suit different organizational needs and security postures. Some of the popular DAM solutions in the market include Imperva, Securonix, AlienVault, and Trustwave.
In conclusion, DAM is a vital technology for database security that provides real-time monitoring and auditing capabilities to detect and prevent cybersecurity threats. DAM helps organizations achieve compliance with regulatory requirements and provides a robust security posture for their databases, which are critical assets in the digital age.