What Is API Authentication and How Does It Work?
API authentication is a vital aspect of securing web applications that use APIs (Application Programming Interfaces) for exchanging information and performing various tasks. It involves the use of digital tokens or keys that allow users and applications to access and use an API’s functionalities, while ensuring that only authorized entities can make such requests.
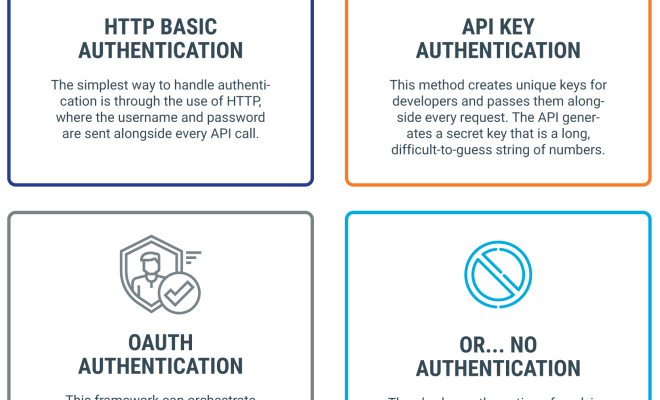
In simpler terms, API authentication enables an API provider to control who is allowed to access its API and what actions those users can perform. There are different authentication mechanisms available for protecting APIs, but most of them work on the principles of authentication and authorization.
Authentication is the process of verifying a user’s identity, while authorization involves granting or denying access to specific resources or functionalities based on the permissions associated with that user. In other words, authentication is about asking “who are you?” while authorization asks “what can you do?”
There are several methods for API authentication, including the use of API keys, OAuth, and JSON web tokens (JWTs). API keys are unique identifiers that are assigned to authorized users or applications and are used to authenticate API requests. OAuth, on the other hand, is an open standard protocol that allows users to grant limited access to their resources without sharing their credentials.
JWTs are an emerging standard that is gaining popularity in API authentication because they offer several benefits over other methods. JWTs are generated by the API provider and contain all the necessary information (such as the user’s identity, permissions, and issue and expiration times) to authenticate and authorize an API request. They are self-contained, meaning they carry all the necessary information without requiring further server access, making them more efficient and scalable.
The process of API authentication involves several steps, which differ depending on the chosen authentication method. Generally, a user or application sends an API request containing an API key or token to the API provider.
The provider then validates the key or token, verifies the user’s identity, and checks the permissions associated with that user to determine if they are authorized to perform the requested action. If the key or token is valid, the API provider responds with the requested data or performs the requested action.
In conclusion, API authentication is a critical component of securing web applications and protecting API resources. By using tokens or keys to authenticate and authorize API requests, providers can ensure that only authorized users and applications can access and use their APIs, providing a secure and reliable user experience.






